The Basics of Developing a Data Security Strategy
We live in a groundbreaking time of technological innovation which increases productivity and financial efficiency betters communication and allows for easier access to information. Unfortunately, this advancement also allows hackers to access networks and data. With botnets, supply-chain attacks, and data breaches happening so frequently, it can make monitoring security while running a business feel nearly impossible. Having a robust data and cybersecurity strategy in place can help alleviate this stress for large corporations, small businesses, and everyone in between.
What is a data and cybersecurity strategy?
A data and cybersecurity strategy is a specific and detailed plan created by an organization to help identify areas of susceptibility, eliminate perceived attacks, as well as monitor and manage issues as they progress. Without a security strategy, networks and data are vulnerable to attacks, and with no plan for how to move forward if an attack occurs, companies are left feeling lost. Whether you have thousands of files with sensitive client information or simply need to protect your small business email account, it is important to have a plan for managing cybersecurity and data protection.
Get everyone on board
Whether you have an entire department dedicated to cybersecurity or you’re a one-person team, security is everyone’s job. This means ensuring every employee has been educated on the fundamental aspects of security required to keep your data safe. From reading emails more carefully to logging out when leaving a device, seemingly small tasks can save you a significant amount of stress, time, and money.
Conduct a data audit
If you collect any information from clients, customers, or vendors they trust you to keep this data secure. Maintaining this trust, as well as meeting any legal requirements, is a must. If you haven’t already, take an audit of the data you collect, where it is stored, who can access it, why they need access, and how often. Doing this allows you to establish a baseline for typical data use and access so you can spot any inconsistencies and address them more quickly.
Know what you are up against
With so many different types of cyber-attacks, it can be hard to keep up, especially if data security isn’t your area of expertise. It is important to learn about multiple types of attacks so you can know which might be the most likely to affect your business. For example, a small retailer might not be the target of a hacker looking to steal sensitive client information to sell, but could be a major target for a disgruntled ex-employee planning to deploy ransomware and make some quick cash.
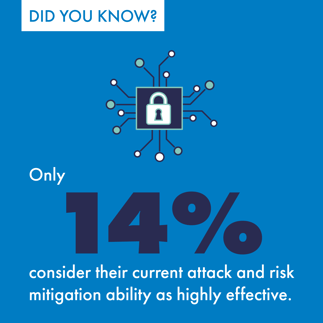
Choose your partners wisely
If you think your business is too small to warrant a cyberattack or need a data security partner, think again. According to the latest research, half of all cyberattacks are aimed at small businesses, yet these businesses are investing very little in their data protection plans. Think of a reliable security partner like a castle with walls. Your business is the castle, and attackers must get through your security partner’s walls before they can even get to you. This moves the threat from your front door to theirs.
Have a disaster recovery plan
Even with the best security plans in place, data breaches can still occur. Your security strategy needs to include a plan for what to do when this happens. This plan should include the data recovery process, your next steps to secure your network after an attack or breach, identifying the source of the attack, and how you plan to inform stakeholders and law enforcement.
It is important to note that while each of these steps is important in developing a data protection strategy, more elements may be necessary for your specific situation. Ritter Communications offers cybersecurity and data recovery services customized to your business. Let us help you build and implement a custom security and data recovery plan




